Cloud Data Protection Platform
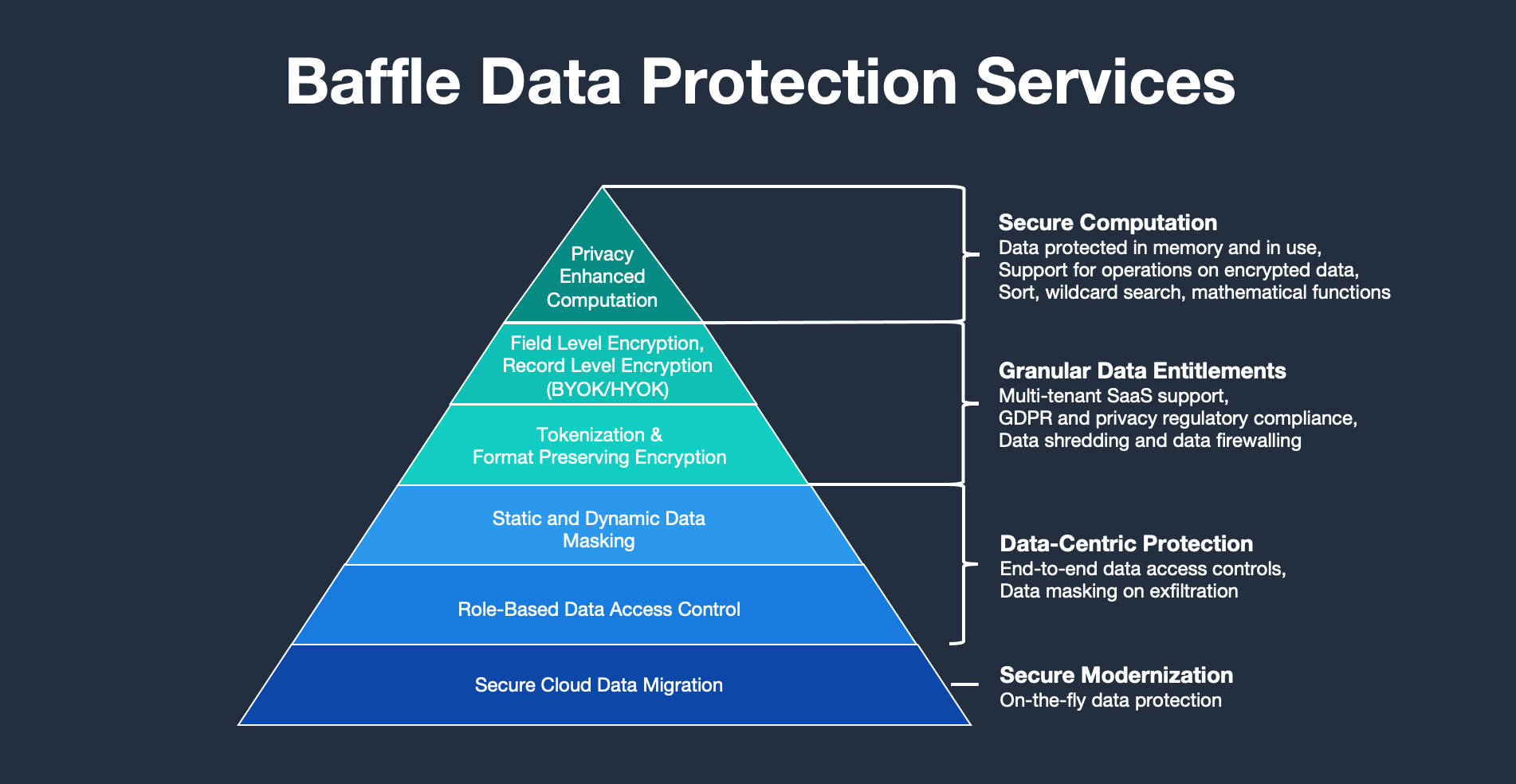
Baffle enables data-centric protection at the field and row level to protect your data in the cloud
Baffle provides a comprehensive Cloud Data Encryption Platform for data security
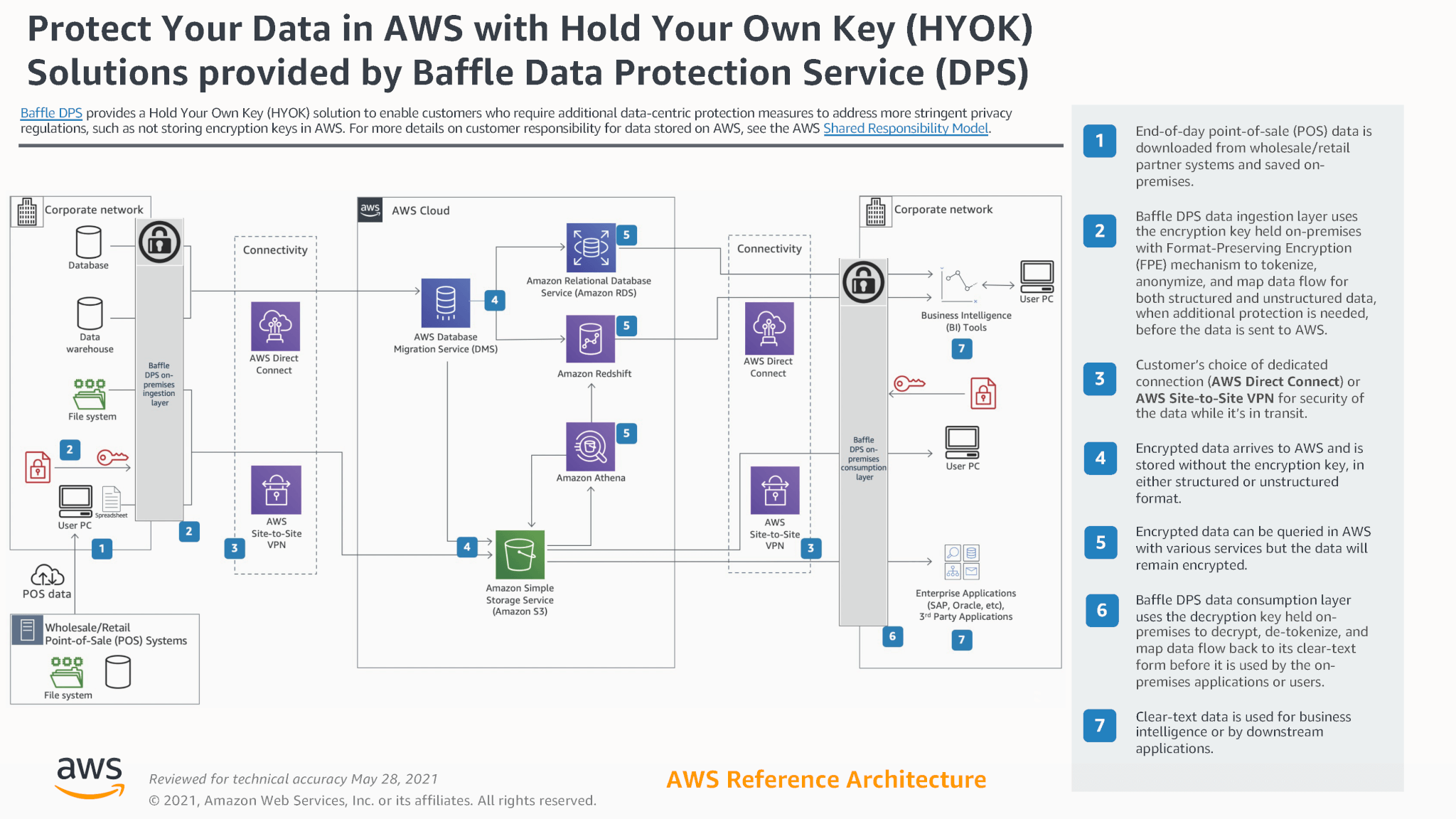
Within the context of the Shared Responsibility Model, the cloud service provider is responsible for protecting the cloud infrastructure that runs all of the cloud services offered by the provider. The customer is responsible, however, for protecting the critical data that they put in the cloud provider’s cloud environment.
Baffle provides a comprehensive Cloud Data Protection Platform (CDPP) to help protect against data loss in the cloud. Baffle’s cloud security solution simplifies encryption, tokenization, and masking of your data in the cloud without requiring any application code modification or embedded SDKs and allowing for vast scalability.
The technology integrates seamlessly with cloud native services and vastly simplifies tokenization and cloud encryption to enable a data-centric security model. The CDPP goes beyond disk and container-based encryption methods, which many data privacy practitioners mistakenly believe is adequate to protect their data for cloud computing. In today's world of security challenges, sophisticated cyberattacks, and data theft, sensitive data needs to be protected by data-centric methods in real-time.
CDPP and data-centric security methods are the last line of defense in a zero-trust security posture. Within the context of zero trust, one assumes that no user or device can be trusted, and this approach assumes that attackers already present in the network have data storage access. Data-centric security measures assume that the same attacker will access your data stores and is integral to protecting your data from attackers. Even when accessed, the data cannot be read as it is encrypted or masked.
Overall, on-premises and cloud data encryption, tokenization, and masking is becoming the standard for businesses secure data and protect resources from outside threats. Therefore, data management and data protection solutions are crucial for Baffle clients. Because with Baffle, they can align security with business and DevOps initiatives to automate and move more workloads to the cloud faster.
Baffle is on a mission to deliver universal data protection and connectivity to protect data wherever it lives. Baffle does all it can to ensure unprotected data is never available to an attacker by assuming that breaches will happen. The company does this by strengthening cloud data security and offering cloud encryption, tokenization, and masking capabilities that protect your data center's sensitive data and mitigate the risks of data theft.
Baffle was founded to battle the increasing threats to enterprise assets in public clouds, private clouds, multi-cloud, and hybrid cloud environments. Our team has strong backgrounds in cloud data encryption, cyber-security, cryptography, storage, and enterprise infrastructure design. Baffle is pioneering a solution that makes data breaches irrelevant by keeping cloud data protected from production through processing.
Read more here on how at-rest encryption and transparent data encryption (TDE) are no longer adequate to protect data in cloud storage against a modern-day attack.
Baffle's data-centric approach combines access monitoring and field-level encryption to provide you with an end-to-end security model to protect against large-scale data breaches.
Baffle’s unique Record Level Encryption (RLE) protects data in multi-tenant SaaS environments and provides granular entitlements to data in co-mingled data stores.
The listing to the right is a partial listing of cloud services that Baffle supports.
Review our reference architecture with Amazon AWS here.
Watch this webinar to learn how data can be easily de-identified as part of your data pipeline as it is staged for use in Snowflake or Amazon Redshift.
Baffle supports the following Infrastructure-as-a-Service (IaaS) providers and deployments:
- Amazon Web Services (AWS)
- Microsoft Azure
- Google Compute Platform (GCP)
- Docker, Kubernetes and container-based deployments
Within AWS, Baffle supports the following platforms and services:
- AWS Aurora MySQL and Postgres
- AWS RDS - MS SQL, MySQL, MariaDB, Postgres
- AWS S3 Object Encryption
- AWS S3 Data Pipeline Encryption
- AWS KMS
- AWS CloudHSM
- AWS Lambda
- AWS ECS Fargate
- AWS Secrets Manager
- AWS Elastic Load Balancer
- AWS Auto Scaling
Equivalent support is offered on other cloud providers.

“Customers are demanding support for Bring Your Own Key (BYOK) to enable ownership of their encryption key material and have control over their data with revocation rights. Workiva is building AWS KMS key management into the core of our platform, where customers can bring in encryption key material and manage it, and then use those keys in conjunction with Baffle. The joint solution requires no large-scale architectural overhauls or application changes, or dedicated databases per tenant. As a result, development time is instead being spent adding even higher value add enhancements instead of modifying the architecture and application, and Baffle allows us to execute on that vision.”
Security Architect, Workiva
Related Resources
Cloud Data Risk: How to Better Protect Your Data in the Cloud
Watch the webinar on Cloud Data Risk: How to Better Protect Your Data in the Cloud. It will cover key tenets of modern data privacy regulations within the context of security controls that are currently available and can be operationalized to improve your company's security posture.
Cloud Misconfigurations: A Surging, but Overlooked Threat
Enterprises continue to migrate their workloads to the cloud with the promise of lower costs, increased agility and greater flexibility. But cloud migration also brings risks, as misconfigured cloud services are one of the fastest-growing sources of data breaches.
Weaving Privacy And Security Into Cloud Migration Is Not Negotiable
A recent study of CIOs offered good news for those concerned about data protection. It reported that 86% of respondents are now viewing security as a higher budget priority, with 68 percent placing the cloud as a higher budget priority.
Our Solution
Baffle delivers an enterprise-level transparent data security platform that secures databases via a "no code" model at the field or file level. The solution supports tokenization, format-preserving encryption (FPE), database and file AES-256 encryption, and role-based access control. As a transparent solution, cloud-native services are easily supported with almost no performance or functionality impact.
Easy
No application code modification required
Fast
Deploy in hours
not weeks
Powerful
No impact to user
experience
Flexible
Bring your own key
Secure
AES cryptographic
protection
Schedule a live demo with one of our solutions experts to get answers to your questions