Blog
Transparent Data Encryption is Not Enough
Security for an earlier time One of the biggest challenges with security is understanding the threats and how to properly defend against them. Just because…
Data Encryption Methods and their Advantages and Disadvantages
Protecting data has become a critical part of every organization’s operation. However, choosing the best method of data encryption can be difficult with all the…
Basics of Data Masking
Asking different people within software organizations or even different people within the security space to define “data masking” often means you will get different –…
Snowflake Data Encryption
There’s no argument that data encryption is a necessary security measure. But when it comes to protecting data on its way to a cloud, is…
Multi-Tenant Data Security for Databases with Record-Level Encryption
Multi-tenant databases are commonly used by SaaS vendors for the sake of cost-efficiency. Having a separate database instance for each of their customers, while ensuring…
Apple Lets Consumers BYOK; Is Your Cloud Provider Following Suit?
Consumers are used to having their messages encrypted end-to-end so that only those with whom they are communicating can see their messages. But, what about…
Top Business Priorities in 2023: Compliance, Data Security, Data Pipelines and Zero Trust
In today’s ultra-competitive business environment, a company’s ability to distance itself from competitors comes down to data—more specifically, the proficiency with which it can analyze…
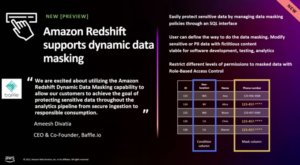
AWS Dynamic Data Masking Announcement Solidifies a Commitment to Complete Data Protection, Data Privacy, and Security
An exciting and promising aspect of being in the data security industry is seeing the adoption of technology by major players that will help businesses…
Redshift Encryption, Security, and Three Questions that Need Answering
Amazon Redshift is used by tens of thousands of clients to analyze data ranging from terabytes to petabytes and to conduct complicated analytical queries. In…
Protecting Data Is Nonnegotiable Today—Does Your Team Have The Skills To Do It?
Not long ago, the security team was a subset of the IT department. Its main objective was to safeguard the IT infrastructure through perimeter protection,…